- cross-posted to:
- selfhosted@lemmy.world
- cross-posted to:
- selfhosted@lemmy.world
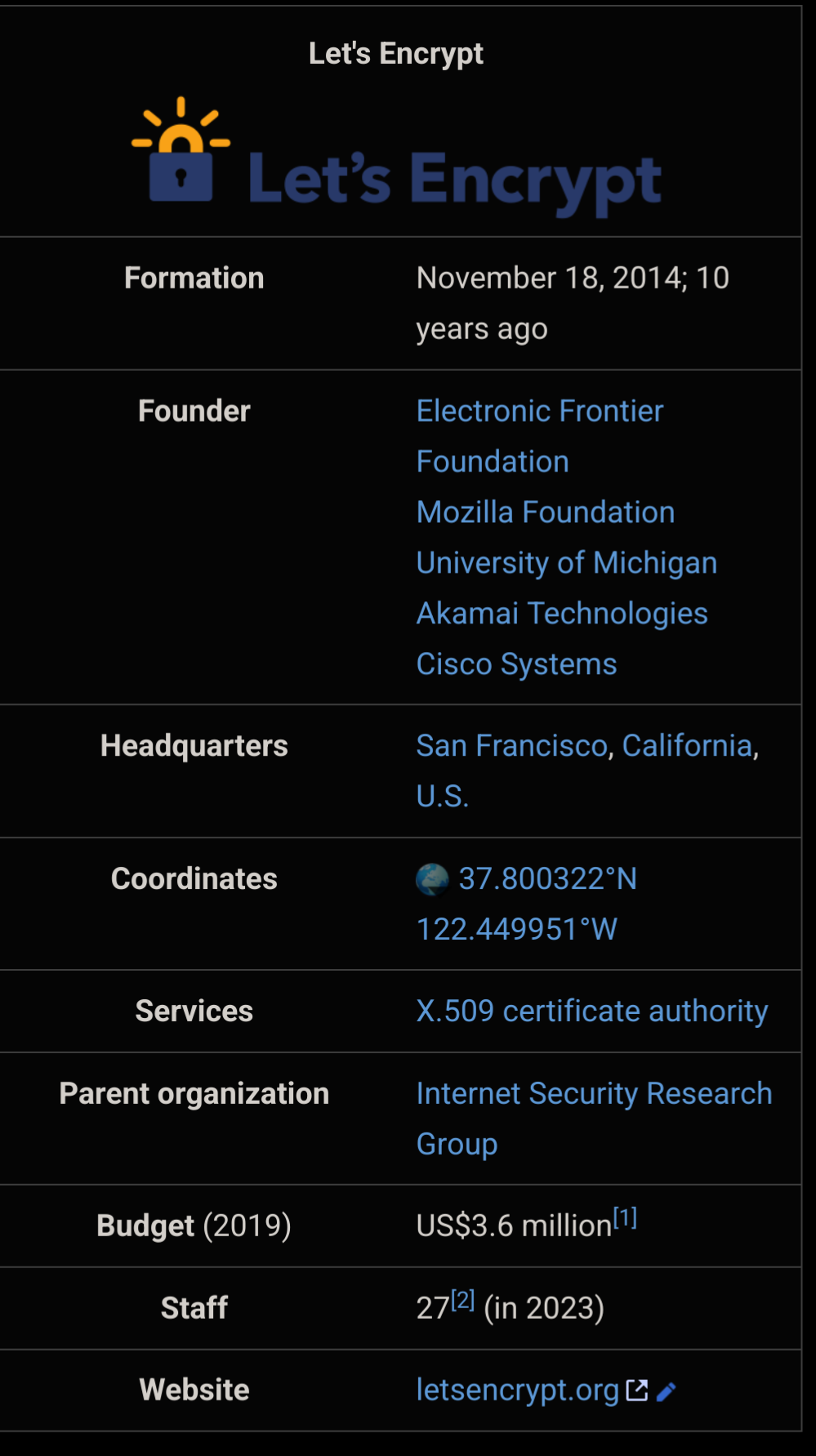
Happy birthday to Let’s Encrypt !
Huge thanks to everyone involved in making HTTPS available to everyone for free !
I worked for a company we had 300 websites, the boss wanted to buy certs. I told him about Lets Encrypt. He loved the idea it saved us a bunch of money. I suggest we donate $100 to them. Hes says “NO F-ing way!”.
And it changed the Internet, for good and a lot.
Huge impact on a tiny budget - that’s extremely impressive. The world could be so much better without rent seeking parasites.
Man I love let’s encrypt, remember how terrible ssl was before the project landed?
Crazy times. Nowadays it’s weird when a website doesn’t have https. Back then it was pretty much big companies only. And the price of a wildcard certificate…
Except for neverssl.com
Triggering the launch of captive portals for public Wi-Fi users everywhere yayy
That website says it will never use SSL, but it definitely just connected over https with a valid certificate when I went there.
That’s odd. Try httpforever.com instead.
Nice yeah that site actively rejects https connections.
I always had to fill out multiple pages of forms to get those free 1 year “trial” certs from startssl.
Oh man, I forgot about startssl until just now. I definitely had a few of those certs. If you wanted something fancy like a wildcard cert back then, you were paying $$$
Luckily, wildcard certs are insecure and should be avoided.
Wildcard certs are perfectly fine. Your own instance lemm.ee is using one right now.
Obviously there could be issues if subdomains are shared with other sites, but if the whole domain is owned by 1 person, what does it matter?
If one system is somehow compromised, the attacker could effectively impersonate all the systems on your entire domain if they had the wildcard cert. Maybe it’s not a huge deal for individuals but for companies or other organisations it could be extremely dangerous.
If someone wanted a wildcard cert at work I would be very cautious before I even considered issuing one. Unfortunately there are a few wildcard certs on our domain, but those are from before my time.
Having a certificate for any subdomain has implications for other sibling domains, even without a wildcard certificate.
By default, web browsers are a lot less strict about Same Origin Policy for sibling domains, which enables a lot of web-based attacks (like CSRF and cookie stealing) if your able to hijack any subdomain
Remember they wanted like $75 for certs? The gall.
And if you remember, that this whole shebang was only started, because Snowden revealed that the NSA spied on all of us, it’s getting much much darker.
People behave as if having a green lock icon were enough to consider you’re safe.
People behave as if there were not multiple cases of abuse of PKI.
People behave as if all those whistleblowing cases exposing widespread illegal activities by the state were not treated as normal, except those exposing them being chased and vilified.
What I’m trying to say is that we’re past the stage where techno-optimism about the Internet made sense. They just say in the news that abusing you is good, and everybody just takes it.
I did not have the money to pay the insane amounts these greedy for-profit certificate authorities asked, so I only remember the pain of trying to setup my self-signed root certificate on my several devices/browsers, and then being unable to recover my private key because I went over the top with securing it.
Can anyone fill me on this? Why is it so significant?
It is the free, easy way to get an SSL cert (plus automated renewals). Without it, maybe HTTPS wouldn’t have been so omnipresent.
And it shouldn’t have been, SSL PKI is an intentionally rigged architecture. It’s intended for nation-states to be able to abuse it.
I’d like much more some kind of overlay encryption over HTTP based on web of trust and what not. Like those distributed imageboards people were trying to make with steganography in emotion.
It’s a trap. Everybody is already in it and it has already been activated, so - the discussion would be of historical interest only.
HTTPS certs used to be very expensive and technically complicated, making it out of reach for most smaller orgs. Let’s Encrypt brought easy mass adoption and changed encryption availability on the web for everyone.
They also made it a open protocol (the ACME protocol), so now there’s a bunch of certificate providers that implement the same protocol and thus can work with the same client apps (Certbot, acme.sh, etc). I know Sectigo and GoDaddy support ACME at least. So even if you don’t use Let’s Encrypt, you can still benefit from their work.
Sleeping too well lately? Consider this:
If LetsEncrypt were to suffer a few weeks outage, how much of the internet would break?
If you have a fully automated setup. Youll have 30 days to mitigate the fallout.
It won’t be that simple.
For starters, you’re assuming t-zero response. It’ll likely be a week before people worry enough that LE isn’t returning before they act. Then they have to find someone else for, possibly, the hundreds or thousands of certs they are responsible for. Set up processes with them. Hope that this new provide is able to cope with the massive, MASSIVE surge in demand without falling over themselves.
And that’s assuming your company knows all its certs. That they haven’t changed staff and lost knowledge, or outsourced IT (in which case they provider is likely staggering under the weight of all their clients demanding instant attention) and all that goes with that. Automation is actually bad in this situation because people tend to forget how stuff was done until it breaks. It’s very likely that many certs will simply expire because they were forgotten about and the first thing some companies knows is when customers start complaining.
LetsEncrypt is genuinely brilliant, but we’ve all added a massive single point of failure into our systems by adopting it.
(Yeah, I’ve written a few disaster plans in my time. Why do you ask?)
Piggybacking off this comment because I completely agree with it.
Did we not learn anything from CrowdStrike? If a comparatively simple fix was able to wipe out half the world, how would something that requires an active choice (where to get certs from) not completely cripple all of our infrastructure?
Damn! That’s definitely a “I’m old” moment for me. I still remember when I first heard about the concept and I remember setting it up the first time on a self hosted project (which seemed harder back then).
Awesome project!
That’s very great news! Thank you for all the good work!
Lol I instinctively freaked out when I saw the post preview assuming it was going to be a post about a major data breach or exploit of some sort relating to Let’s Encrypt.
I probably need more positivity in my life 😂
Let’s Encrypt is amazing, but are there any equally trustworthy alternatives people could switch to if something bad happens to it?
If it begins to enshitify, someone will quickly take up the helm. It’s become so core now that someone like Cloudflare would just be like “We do this now.”
I think Cloudflare enshittifying is a bigger risk that Let’s Encrypt.
Cloudflare sort of provides this now by being a MITM to secure your site between your server and the end user. But this requires you and your end user to trust Cloudflare.
And fwiw the ACME protocol is open so anyone can implement it. I believe even the ACME software that EFF sends out allows you to choose your server with some configuration.
ZeroSSL, plus a few paid companies support ACME (I know Sectigo and GoDaddy do). Sure, the latter are paid services, but in theory you can switch to them and use the exact same setup you’re currently using with Let’s Encrypt.
Maybe ZeroSSL
They don’t offer wildcard certs, but otherwise I think they are.
I wanna say acme.sh defaults to them.Never used them, but they state at https://zerossl.com/features/acme/ that their free acme certs include wildcards.
Yes, seems you are right. Not sure where I got the impression.
Unrelated, when I researched this I saw that acme.sh, zerossl, and a bunch of other acme clients are owned by the same entity, “Stack Holdings”/“apilayer.com”. According to this, zerossl also has some limitations over letsencrypt in account requirements and limits on free certificates.
By using ZeroSSL’s ACME feature, you will be able to generate an unlimited amount of 90-day SSL certificates at no charge, also supporting multi-domain certificates and wildcards. Each certificate you create will be stored in your ZeroSSL account.
It is suspicious that they impose so many restrictions then waive most on the acme api, where they presumably could not compete otherwise. On their gui they allow only 3 certificates and don’t allow multi-domain at all. Then even in the acme client they somehow push an account into the process.
[…] for using our ACME service you have to create and use EAB (External Account Binding) credentials within your ZeroSSL dashboard.
EAB credentials are limited to a maximum per user/per day. [This might be for creating them, not uses per credential, unsure how to interpret this.]
This all does make me slightly worry this block around apilayer.com will fall before letsencrypt does.
Other than letsencrypt and zerossl, this page also lists no other full equivalents for what letsencrypt does.
They came up with the ACME protocol, so presumably somebody could. The real barrier to entry is the cost of getting into that certificate chain of trust. I have no idea why it’s so difficult and expensive.
Well, it’s difficult, as it should be, because if you control a certificate in the active chain of trust of browsers, you can hack pretty much anything you want.
Correct me if I’m wrong, but isn’t the CA only signing your public key to prove identity/authority? I don’t think the CA can magically MITM every cert they sign.
The impact is serious enough to warrant a $1m entry fee, IMO. At best, someone could impersonate a site. They’d also have to get other things in line (e.g. DNS hijacking) to be at all successful anyway. And it’s not like most people are authenticating certs themselves. They just trust browsers to trust CAs that vouch for you and prevents those scary browser warnings.
It doesn’t improve encryption compared to a self-signed cert though.
If you are the CA, you can sign a new certificate yourself for google.com and the browser will accept it. It’s effectively allows MITM for any certificate. Worse, it’s not even limited to certificates under that CA. The browser has no way of knowing there’s 2 “valid” certs at once, and in fact that is allowed regardless (multiple servers with different instances of the SSL cert is a possibility).
Certificate pinning might save things, since that will force the same certificate as was previously used, but I’m not sure this is a common default.
Underrated. Stuff rocks.
SSL Certs were so god awful before certbot that it’s hard to explain now that it’s so easy and free.
Also fucking expensive
Just two months ago, a security team member dinged one of our services for using Lets Encrypt, as “it’s not as secure as a traditional CA”.
I’d love for them to explain how, if anything the short cert validity and constant re-checking of the domain seems more secure than traditional CAs
I’d also argue that the fact that it’s automated and their software is open source makes it objectively more secure. On the issuing side, there’s no room for human error, social engineering, etc.
It’s sad that these arguments are still being shared. It was the same arguments years ago from people that would just assume that a free cert was inherently unsafe.
Lots of people shitting on stories of people who buy certs.
You do still have to buy a cert if you want one for a .onion. Let’s encrypt still doesn’t support it :(
I’m also having to manually cert every 3 months for my emby instance. It’s a minor inconvenience, but I’m definitely tempted to just buy a yearly.
Emby?
Same idea as Jellyfin / Plex. Self hosted media server. Plex handles ssl certs for you, Emby doesn’t have an automatic process so I’m having to manually replace it every 90 days
Why not use a reverse proxy with this built in? Caddy, Traeffik…
Why not script it so you don’t have to do it manually?
Your advice is sound, my ability to focus on such a task however… lol
But…an onion address doesn’t need a cert?
Some apps refuse to work if you dont have TLS, so it depends what you’re running
I’m sad to say that all my sites where http only until 10 years ago














